In the process of troubleshooting an issue of two different customers with very little in common (different countries, different web hosts, different macOS versions, different different project files), after much head scratching, we found something unexpected and surprising.
The symptom was the site was rather broken (missing images mainly). Upon digging a bit more we found that a supporting Javascript file (jquery.xxxx.js) was badly mangled. Specifically the first 64K bytes of the original file were at the end of the server file, with the rest at the beginning.
We ran through many hypothesis:
- a server cache issue of some kind
- a broken Sparkle.app
- a broken file transfer library in Sparkle 3.1
- a broken FTP server
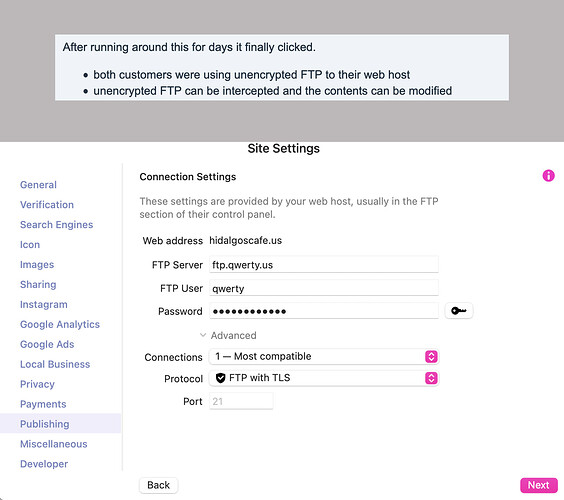
After running around this for days it finally clicked.
- both customers were using unencrypted FTP to their web host
- unencrypted FTP can be intercepted and the contents can be modified
- some types of malware presumably intercept and upload malware by modifying javascript on the fly (I’m not a security expert so I don’t know how many)
- for that reason antivirus software intercepts all outgoing FTP traffic and checks it for malware
- if antivirus software has bugs, it will affect anything you transfer to your server
As it turns out both customers had Norton 360 installed, and a quick check by deactivating it solved all publishing issues.
I personally don’t use antivirus software, but I also don’t download stuff from questionable places and don’t have a big corporation imposing an antivirus as a policy on me.
My suggestion is not to uninstall or disable antivirus software if you can’t, rather to ensure that the connection from Sparkle to your server is encrypted, either SFTP or FTP with TLS. This prevents antivirus software from snooping into and corrupting your transfers.
Sparkle does warn you about using an insecure FTP connections, it’s a more serious issue than it seems!
This problem wasted many engineering hours that we’ll never get back, for a bug we didn’t create and we have no way to fix, I find this kind of antivirus behavior to be inexcusable.